-
-
Notifications
You must be signed in to change notification settings - Fork 95
LeechAgent
The LeechAgent is an agent running, on a remote computer, as a service (or ordinary program in interactive mode) The LeechAgent communicates over port tcp/445 or tcp/28473. The LeechAgent exists for 32-bit and 64-bit Windows. The LeechAgent currently does not exist for non-Windows platforms.
The LeechAgent accepts, by default, incoming connections from clients whose users are administrators on the system running the LeechAgent. Mutual authentication and encryption are provided, by default, by active directory based kerberos - making the user experience completely seamless. It's also possible to connect using NTLM - primarily to non-domain joined computers.
Download the latest pre-packaged LeechAgent from the LeechCore releases section. The LeechAgent comes pre-packaged with WinPMEM for memory acquisition and MemProcFS for remote memory analysis.
The LeechAgent allows for simultaneous client connections from applications such as PCILeech and MemProcFS.
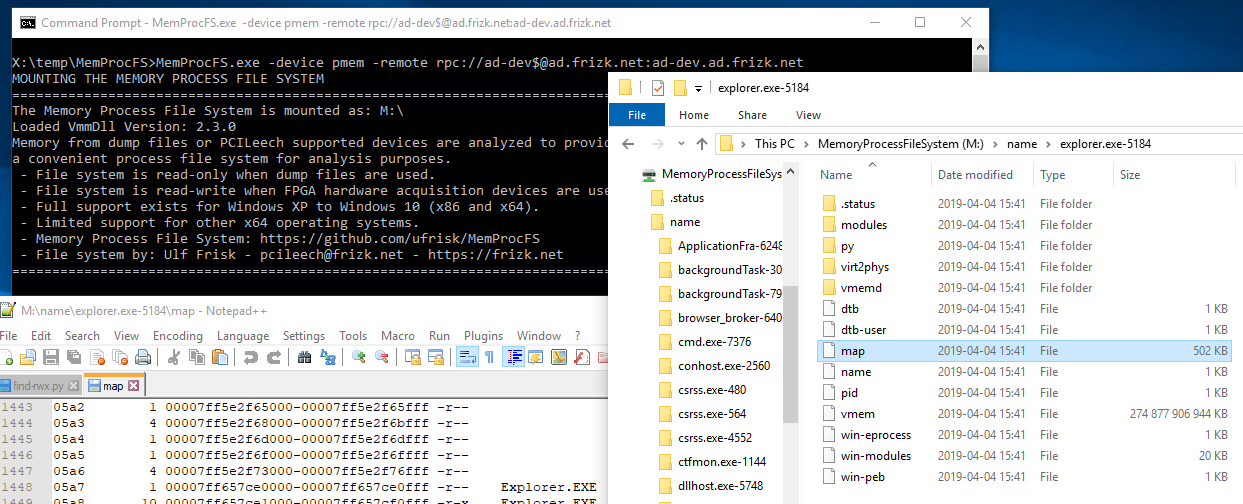
Connected applications may access and dump physical memory of the system running the LeechAgent. It's possible for the LeechAgent to acquire memory using any acquisition method supported by the LeechCore library. This includes host system memory via WinPMEM and VM memory from VMWare or Hyper-V. The image below shows MemProcFS instance connected to a remotely installed LeechAgent.
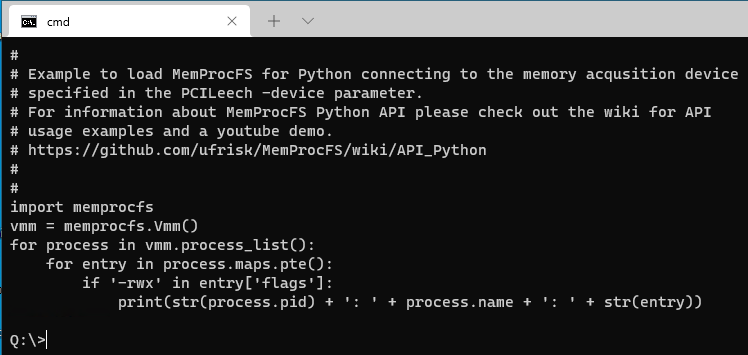
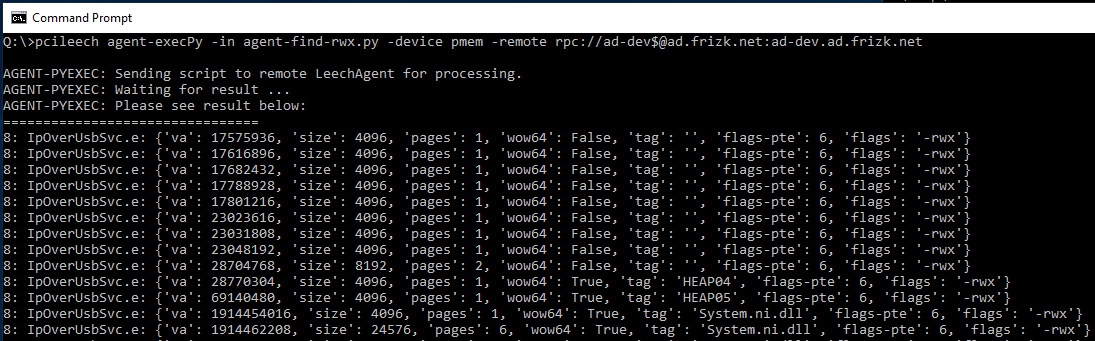
Execute MemProcFS memory analysis scripts coded in Python on the remote LeechAgent host. Python analysis scripts submitted by remote clients are able to make use of the full MemProcFS Python API and the local physical memory of the host running the LeechAgent. This works extremely well for fast and efficient physical memory analysis even over high-latency low-bandwidth connections. The scripts will be executed in-memory and will never touch disk on the remote system. The remote scripting capabilities currently exists only for the 64-bit version of the LeechAgent. The pictures below show a sample analysis script submitted to the remote LeechAgent for analysis.
It's possible to run MemProcFS analysis on the remote host - giving extremely fast access to the local remote memory. File system calls are proxied to the remote host. Only file listings, reads and writes in the virtual file system are transmitted over the network resulting in an extremely efficient low-bandwith memory analysis.
Read more about MemProcFS Remoting on the MemProcFS wiki.
The default recommended way of running the LeechAgent is as a service. For information about installing it please visit the wiki entry about Installing the LeechAgent.
It's possible to run the LeechAgent in interactive non-service mode. If running in interactive mode the -insecure flag may optionally be specified.
Interactive mode is useful for testing, or if the DumpIt memory acquisition method is used to acquire live memory.
If running in insecure mode no authentication takes place - anyone with network access to the
port tcp/445 or tcp/28473 may connect and start acquiring memory. Also the connection between the client and server won't be encrypted over the network. Furthermore, no logging to the event log will take place. Insecure mode may be useful for testing or if the target computer is not a part of an active directory domain.
If using DumpIt or WinPMEM to acquire memory remember to start the application as elevated administrator.
Start the LeechAgent as a stand-alone non-service executable in interactive mode using standard kerberos-secured authentication.
LeechAgent.exe -interactive
Start the LeechAgent as a stand-along non-service executable in interactive mode insecure (no security) mode - allowing anyone with network access to port tcp/445 or tcp/28473 to connect to acquire physical memory and also to execute arbitrary code as the current user.
LeechAgent.exe -interactive -insecure
Start the LeechAgent in interactive no-security mode using DumpIt - allowing anyone with network access to port tcp/445 or tcp/28473 to connect to acquire physical memory and also to execute arbitrary code as the current user.
DumpIt.exe /LIVEKD /A LeechAgent.exe /C "-interactive -insecure"
In the examples it is assumed that:
- The
LeechAgentis installed as a service on the computerinfected.evilcorp.com. - In the
evilcorp.comactive directory domain. - WinPMEM and Embedded Python is co-bundled in the LeechAgent remote install.
- The connecting user is an administrator on the target computer.
pcileech.exe -device pmem -remote rpc://[email protected]:infected.evilcorp.com agent-execpy agent-find-rwx.py
MemProcFS forensic memory analysis remotely and retrieve the elasticsearch compatible result to the C:\Temp directory:
pcileech.exe -device pmem -remote rpc://[email protected]:infected.evilcorp.com agent-elastic -out C:\Temp\
Use MemProcFS to analyze the remote system (analysis locally, memory acquisition from remote system) Authenticate using NTLM:
memprocfs.exe -device pmem -remote rpc://ntlm:infected.evilcorp.com
Use MemProcFS to analyze the remote system on a non-domain joined computer. NTLM authentication. Username/Password prompt:
memprocfs.exe -device pmem -remote rpc://ntlm:infected.local:logon
Use MemProcFS Remoting to analyze the remote system (analysis and memory acquisition on the remote system). Connect over SMB port 445.
memprocfs.exe -device pmem -remote smb://[email protected]:infected.evilcorp.com -remotefs
Sponsor PCILeech and MemProcFS:
PCILeech and MemProcFS is free and open source!
I put a lot of time and energy into PCILeech and MemProcFS and related research to make this happen. Some aspects of the projects relate to hardware and I put quite some money into my projects and related research. If you think PCILeech and/or MemProcFS are awesome tools and/or if you had a use for them it's now possible to contribute by becoming a sponsor!
If you like what I've created with PCIleech and MemProcFS with regards to DMA, Memory Analysis and Memory Forensics and would like to give something back to support future development please consider becoming a sponsor at: https://github.com/sponsors/ufrisk
Thank You 💖